10 Most Dangerous Hackers In History
Best Hacker In History on April 2024 Shopping Deals at Bestonio.com
-
The Divided Welfare State: The Battle over Public and Private Social Benefits in the United States
- UPC: 884796905974
- ASIN: 0521013283
- ISBN: 0521013283
- Manufacturer: Cambridge University Press
The Divided Welfare State is the first comprehensive political analysis of America's distinctive system of public and private social benefits. Everyone knows that the American welfare state is unusual--less expensive and extensive, later to develop and slower to grow, than comparable programs abroad. Yet, U.S. social policy does not stand out solel... [Read More]
-
The Innovators: How a Group of Hackers, Geniuses, and Geeks Created the Digital Revolution
- ASIN: 1476708703
- ISBN: 1476708703
- Brand: Simon & Schuster
- Manufacturer: Simon & Schuster
Following his blockbuster biography of Steve Jobs, Walter Isaacson’s New York Times bestselling and critically acclaimed The Innovators is a “riveting, propulsive, and at times deeply moving” (The Atlantic) story of the people who created the computer and the Internet.What were the talents that allowed certain inventors and entrepreneurs to t... [Read More]
-
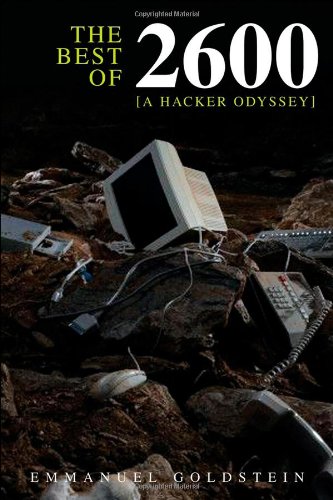
The Best of 2600: A Hacker Odyssey
- ASIN: 0470294191
- ISBN: 0470294191
- Brand: Wiley
- Manufacturer: Wiley
Since 1984, the quarterly magazine 2600 has provided fascinating articles for readers who are curious about technology. Find the best of the magazine’s writing in Best of 2600: A Hacker Odyssey, a collection of the strongest, most interesting, and often most controversial articles covering 24 years of changes in technology, all from a hacker’s ... [Read More]
-
The Kids Book of Canadian History
- ASIN: 1554533287
- ISBN: 1554533287
- Brand: Kids Can Press
- Manufacturer: Kids Can Press
Canada has a rich and fascinating history. In this informative overview, kids will discover the people, places and events that have shaped our country. Featuring fact boxes, mini-profiles, maps, a timeline and more, this title in the acclaimed Kids Book of series offers a comprehensive and engaging look at Canada's development, change and growth. K... [Read More]
-
Tie Hackers to Timber Harvesters: The History of Logging in BC's Interior
- ASIN: 1550171895
- ISBN: 1550171895
- Brand: Brand: Harbour
- Manufacturer: Harbour
The first complete history of logging in BC's interior documents the characters, companies and innovations that have helped make BC a world leader in the forest products industry. This large-format book includes more than 200 historical photographs and scores of oral histories from the loggers, millworkers and policy-makers who made the industry wh... [Read More]
-
The 1-Page Marketing Plan: Get New Customers, Make More Money, And Stand out From The Crowd
- ASIN: 1989025013
- ISBN: 1989025013
- Manufacturer: Page Two
WARNING: Do Not Read This Book If You Hate Money To build a successful business, you need to stop doing random acts of marketing and start following a reliable plan for rapid business growth. Traditionally, creating a marketing plan has been a difficult and time-consuming process, which is why it often doesn’t get done. In The 1-Page Marketing ... [Read More]
-
Mindf*ck: Cambridge Analytica and the Plot to Break America
- ASIN: B07VP1T786
- Manufacturer: Random House
For the first time, the Cambridge Analytica whistleblower tells the inside story of the data mining and psychological manipulation behind the election of Donald Trump and the Brexit referendum, connecting Facebook, WikiLeaks, Russian intelligence, and international hackers. Mindf*ck goes deep inside Cambridge Analytica’s “American operations,�... [Read More]
-
The Cuban Cigar Handbook: The Discerning Aficionado's Guide to the Best Cuban Cigars in the World
- ASIN: 160433620X
- ISBN: 160433620X
- Brand: Cider Mill Press
- Manufacturer: Cider Mill Press
The Most Definitive Guide to Cuban Cigars!For more than two centuries, Cuban cigars have been heralded as the best cigars in the world. More than just a cigar, they're an art form, with tobacco growers and hand-rollers considered artists. Today, there are more than 200 varieties to discover, and this essential guide highlights each one. Featu... [Read More]
-
The Art of Invisibility: The World's Most Famous Hacker Teaches You How to Be Safe in the Age of Big Brother and Big Data
- ASIN: B01GZY28CW
- Manufacturer: Little, Brown and Company
Be online without leaving a trace.Your every step online is being tracked and stored, and your identity literally stolen. Big companies and big governments want to know and exploit what you do, and privacy is a luxury few can afford or understand.In this explosive yet practical book, Kevin Mitnick uses true-life stories to show exactly what is happ... [Read More]
-
Womens Russian Hacker in Cyrillic, Funny Cyber Espionage Warfare V-Neck T-Shirt
- ASIN: B07YPJKR29
- Brand: Funny Russia and Propaganda Apparel
- Size: Small
- Manufacturer: Funny Russia and Propaganda Apparel
Click and check out our brand "Funny Russia and Propaganda Apparel" for more funny Russian spy clothing
-
Cisco ASA5506-K9= Network Security Firewall Appliance
- UPC: 193808121838
- ASIN: B00UV073AE
- Brand: Cisco
- Manufacturer: Cisco Traders 1824990
Meet the industry's first adaptive, threat-focused next-generation firewall (NGFW) designed for a new era of threat and advanced malware protection. Cisco ASA with FirePOWER Services delivers integrated threat defense for the entire attack continuum - before, during, and after an attack. How? By combining the proven security capabilities of the Cis... [Read More]
-
The Ultimate Cigar Book: 4th Edition
- ASIN: 1632206579
- ISBN: 1632206579
- Brand: Skyhorse
- Manufacturer: Skyhorse
The Ultimate Cigar Book is a classic on the subject, covering everything from how cigars are made, to storage, etiquette, and accessories.Richard Carleton Hacker’s category bestselling is often credited with helping to create a new generation of cigar aficionados. No other book contains as much detailed and factual information on virtually every ... [Read More]
-
Crypto: How the Code Rebels Beat the Government Saving Privacy in the Digital Age
- ASIN: 0140244328
- ISBN: 0140244328
- Manufacturer: Penguin Books
If you've ever made a secure purchase with your credit card over the Internet, then you have seen cryptography, or "crypto", in action. From Stephen Levy—the author who made "hackers" a household word—comes this account of a revolution that is already affecting every citizen in the twenty-first century. Crypto tells the inside story of how a gr... [Read More]
-
BookFactory Password Journal/Password Organizer/Password Book/Logbook/Password Keeper, 120 Pages, 3 1/2" x 5 1/4", Durable Thick Translucent Cover, Wire-O Binding (JOU-120-MCW-A-(Password))
- ASIN: B009YK2GOA
- Brand: BookFactory
- Manufacturer: BookFactory
Durable Translucent Cover Custom Password Journal with spaces to record Web Site, Email Used, Username, Password(s) and Notes
10 Most Dangerous Hackers In History
5 Most Dangerous Hackers Of All Time
दुनिया के 10 सबसे खतरनाक हैकर्स || 10 Most Dangerous Hackers of all time
© Bestonio.com - all rights reserved - Sitemap Bestonio.com is a participant in the Amazon Services LLC Associates Program, an affiliate advertising program designed to provide a means for sites to earn advertising fees by advertising and linking to Amazon.com




![Hacksaw Ridge 4K Ultra HD [Blu-ray + Digital HD]](https://images-na.ssl-images-amazon.com/images/I/51z5G-EqW2L.jpg)